Filter by topic and date
ACME: Universal Encryption through Automation
- Richard Barnes
- Jacob Hoffman-Andrews
- Daniel McCarney
12 Mar 2019
The Automated Certificate Management Environment (ACME) protocol, recently published as RFC 8555, lets you set up a secure website in just a few seconds.

When you connect to your bank or your health care provider over the Internet, you need to know that you’re actually talking to them, and not a bad actor who is impersonating them and might steal your information or tamper with the transaction. Security protocols such as TLS 1.3 provide encryption that protects you from everyone except the other side of the connection, but don’t themselves allow you to verify who that person is.
To verify that the other side of the connection is who you think it is, we typically rely on a “public key infrastructure” (PKI). Using PKI technologies, the entities you interact with on the Internet get digital “certificates” from Certificate Authorities (CAs). These certificates let them prove their identity to you when you connect to them.
For a long time, though, the need for digital certificates made it harder for people to deploy TLS. This is because getting a certificate for a web server has always been a very manual process—the owner of the web server in question had to go to a CA’s web site, enter a bunch of information, take some steps to prove they control the domain name, wait for the certificate to be issued, and then finally download their certificate and install it on the web server. It was a complex and error-prone process that cost lots of valuable time for system administrators.
The ACME protocol, recently published as RFC 8555, changes all that. With ACME, you can set up a secure website automatically, in just a few seconds.
ACME takes all those steps that an administrator has to do and makes them automatic. Instead of filling information into a form on the web and following written instructions, the server that needs a certificate can send in its information in a standard form, and get instructions that it can read and follow automatically. In many cases, this allows a server to get a certificate more or less instantly and with no human intervention at all, so that security can be on by default.
Back in 2015, Let’s Encrypt created a new Certificate Authority using an early draft of ACME, which let people start experimenting with the protocol. Through the IETF’s open process, ACME was updated to incorporate feedback from other CAs and users of certificates, and today several CAs have ACME interfaces either in production or in development, including BuyPass, Entrust, DigiCert, and Sectigo. Together, these CAs account for the majority of the certificates used on the Internet; Let’s Encrypt alone uses ACME to issue more than a million certificates per day.
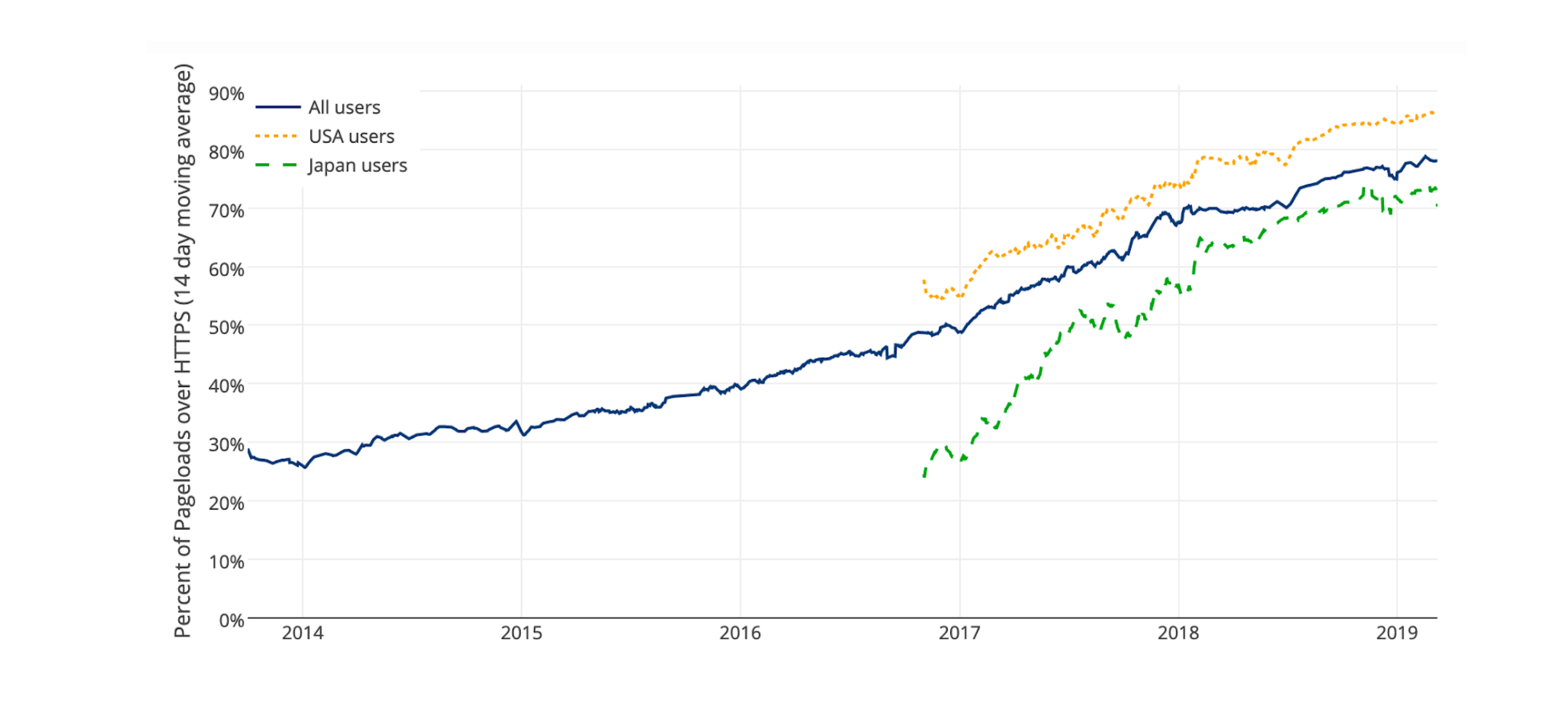
The automation enabled by ACME unlocks the potential for universal encryption on the Internet. When Let’s Encrypt launched in 2014, less than 30% of web requests were encrypted with HTTPS. Today, that number is nearly 80%. The publication of ACME as an IETF RFC and its adoption by more and more CAs will help bring us closer to closer to ensuring all communications on the Internet are confidential and authentic.
Bibliography
[1]RFC 8555
Automatic Certificate Management Environment (ACME)
Public Key Infrastructure using X.509 (PKIX) certificates are used for a number of purposes, the most significant of which is the authentication of domain names. Thus, certification authorities (CAs) in the Web PKI are trusted to verify that an applicant for a certificate legitimately represents t…